TL;DR
Introduction
You might be wondering how you can have a blog without a database. In true Jekyll style, blogging is powered by text files only. Blog posts live in a folder called _posts. The filename for posts have a special format: the publish date, then a title, followed by an extension.
Create your first post at _posts/2018-08-20-bananas.md with the following content: Jekyll requires blog post files to be named according to the following format:
Top 5 to consider
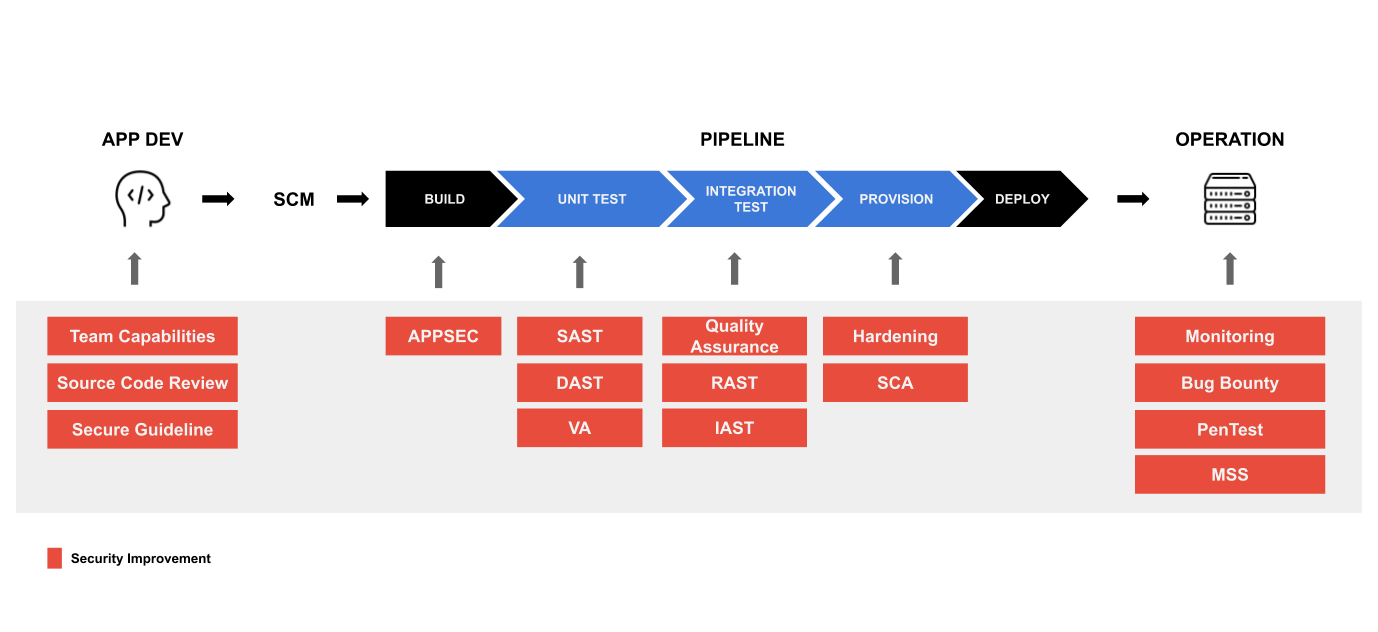
Team capabilities
Good teams are ambition and assets of company, we need to build security awareness in team.
Security guideline
Bounch of security guideline out side, we can choose the most fit for us like HIPPA, PCI, OJK and OWASP should be part of business security risk guildeline.
Implementation capabilities
-
Static Application Security Testing (SAST): Prevents vulnerabilities early in the development process, allowing them to be fixed before deployment
-
Dynamic Application Security Testing (DAST): Once code is deployed, prevents exposure to your application from a new set of possible attacks as you are running your web applications
-
Dependency Scanning: Automatically finds security vulnerabilities in your dependencies while you are developing and testing your applications, such as when you are using an external (open source) library with known vulnerabilities
-
Container Scanning: Analyze your container images for known vulnerabilities
-
Auto Remediation: Auto remediation aims to automated vulnerability solution flow, and automatically create a fix. The fix is then tested, and if it passes all the tests already defined for the application, it is deployed to production.
-
Secret Detection: Prevent secrets from accidently leaking into your Git history. Each commit is scanned for secrets within SAST.
-
IAST and Fuzzing: Future features GitLab will be adding to its Security capabilities, see the visions for IAST and Fuzzing
-
much more
Penetration
Make sure all environment, applciation and servers are passed from penetrate before lounch. We can do several activity like:
- Penetration test(Pentest)
- Bug Bounty
- Continuous test
Secure monitoring
To make sure production ready, provide secure monitoring to monitor and indentify attact. be safe
Contact Us
If you have any questions and comment, please contact us via our contact form.